Sorry for the late reply about the BSOD issue (especially in this thread), but here is my debugging information, from BlueScreenView;
==================================================
Dump File : 071115-33031-01.dmp
Crash Time : 11/07/2015 08:56:46 pm
Bug Check String : BAD_POOL_CALLER
Bug Check Code : 0x000000c2
Parameter 1 : 00000000`00000007
Parameter 2 : 00000000`00001200
Parameter 3 : 00000000`0c000000
Parameter 4 : ffffe001`f29be558
Caused By Driver : tcpip.sys
Caused By Address : tcpip.sys+1c2180
File Description : TCP/IP Driver
Product Name : Microsoft® Windows® Operating System
Company : Microsoft Corporation
File Version : 6.3.9600.16384 (winblue_rtm.130821-1623)
Processor : x64
Crash Address : ntoskrnl.exe+150ca0
Stack Address 1 :
Stack Address 2 :
Stack Address 3 :
Computer Name :
Full Path : C:\WINDOWS\Minidump\071115-33031-01.dmp
Processors Count : 4
Major Version : 15
Minor Version : 9600
Dump File Size : 281,456
Dump File Time : 11/07/2015 08:57:50 pm
==================================================
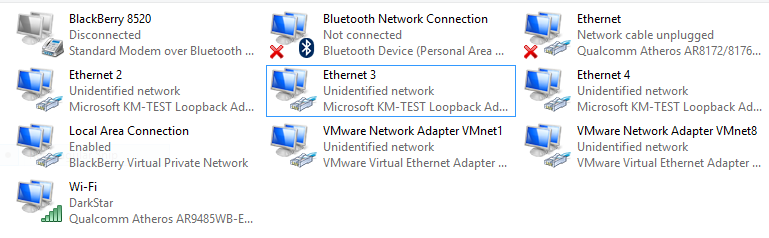
I don't know if they're related to NPCap, or WinPCap (since BSV seems to load the current executable/DLL images from disk, to resolve the vendor names; and the nature of npf.sys is that it's always RAM-resident, and loaded into the TCP/IP stack), but I also have MiniDumps with SYSTEM_SERVICE_EXCEPTION, and SYSTEM_THREAD_EXCEPTION_NOT_HANDLED errors.
Tyson.